Wow, I can't believe I haven't been blogging for more than 3 years already.... time went so fast, just too fast... until someone reminded me.. "Mieke, you know you still have a blog - why don't you update it with some news?".
Honestly - I totally forgot about my blog, as I am not a writer or anything else in between, but I do feel guilty for not "maintaining" this anymore. Thanks to my followers for keeping up with me ;-)
So Yes, I'm still alive and trying to kick (malware) asses - but more in the background as that's where I prefer to stay - out of the picture.
The fact that I don't blog anymore is mainly because I just don't always have the time for it. There's always something new, challenges that keep me away from this. My work environment has become so interesting... and challenging.
But yes, I should maintain this more often with sense and nosense about malware or anything else in between, so I promise I'll do my best to update my blog more frequently.
Monday, May 16, 2016
Back to the future (nowadays)
Saturday, February 16, 2013
Unwanted or wanted toolbars, when to detect..
This is a follow up on a previous blogpost of me: http://miekiemoes.blogspot.be/2012/01/unwanted-toolbars.html
I received a lot of feedback on this (mainly via mail) which was an eye-opener....
We can't ignore the fact that more and more free software is bundled with an additional toolbar or software to cover the costs. After all, developing & have the bandwith available for downloading the software isn't free, so it's understandable they need some sort of coverage for the costs.
The affiliate who offers the most is obviously being used more frequently into bundled installs.
In most (almost all) cases, when a user installs the software, they are presented with options whether they want - or do not want to install this additional certain software bundle. Since, in most (almost all) cases, this is pre-selected by default, people don't bother with the install screens, don't read and just click "next" and "next".
Then, in the end, they are complaining about an additional toolbar/startpage/searchpage they never wanted.
This is exactly why I can't stress enough to read "install screens" while you're installing a program. If you don't want the additional crap, just unselect from the install screens. In case you have installed it already, in most cases, it's easy to uninstall them again. Most of these affiliates have additional uninstall/remove instructions on their site.
Alot of these toolbars or additional software is harmless though - you can basically compare them with the "google" - or "yahoo" toolbar (although there are some exceptions).
This is why I would love to hear your thoughts on this. Should an AV-Vendor detect such (harmless) toolbars or not? Basically, when to detect - or when not to detect?
Tuesday, December 18, 2012
Toys for Xmas
I've listed some "must have" goodies for the geeks among us for 2013. Probably, most of you have these goodies already, but in case you don't, it may be a good idea to put on your Xmas list.
* USB3 & USB3 & more USB3 If you're planning to buy a new PC or laptop or anything else with USB ports, please make sure you have at least 1 or 2 USB3 ports. While USB3 was released in November 2008 already, we now start to see more units with USB3 ports/support. USB3 is much faster than USB1 or USB2 and they are still backwards compatible with older USB ports. Basically, it's almost 10 times faster than USB2. If you want to buy a flash drive, get a USB3 flash drive. It's still more expensive than USB2, but it's really worth the price (which will drop soon anyway). Ofcourse, you gain most from this if you connect from a USB3 port. Most (if not all) new units are supported/have USB3 ports now anyway, so this is one of the reasons why you should stop buying USB2 flash drives or anything else USB2-ish :D * Replace old drives with an SSD (Solid State Drive). Many of you probably have old PCs/laptops and you want to give it some boost/power. Adding RAM is a good option, but you may want to consider to replace your HDD with an SSD. Solid State Drives are faster than conventional spinning drives because they have no moving parts. The storage on an SSD is handled by flash memory chips. Advantages are less power usage, higher reliability and faster access to your data. They are also less resistant to shocks and vibration. In general, when you install an SSD, the first immediate benefits are faster application load time and faster boot time. SSDs aren't cheap, but really worth the price. Disadvantage is, you have less data storage than a conventional HDD (comparison size/price with HDD), but if storage isn't a real problem for you - then you really might want to consider an SSD. After all, you can still combine it with an internal or external HDD to store your data. SSDs have dropped in price to the point where it's affordable to replace your laptop or PC HDD. Normally, a 128GB SSD should suffice your storage needs (just compare with the current storage you need/have) - but a 256GB SSD is even better. You can have larger SSDs as well ofcourse. You can read more about SSDs here: http://en.wikipedia.org/wiki/Solid-state_drive and here: http://lifehacker.com/5932009/the-complete-guide-to-solid+state-drives You can also easily migrate your Windows installation from an HDD to an SSD without losing any data or reinstalling Windows. There are a lot of tutorials on the net for that.But I personally prefer to start from scratch to avoid any issues. In either way, there's a good tutorial here: http://lifehacker.com/5837543/how-to-migrate-to-a-solid+state-drive-without-reinstalling-windows * Get a docking station for your SATA drives with USB support This is really a MUST HAVE! I am sure many of you have come in situations where your HDD wouldn't boot, or you want to mount a drive that has failed. For many (inluding me), it's a hassle to mess around with adding the drive as a slave to your PC in order to get access to the data and transfer/alter/delete. This is exactly one of the reasons why I bought this. Just slide in your SATA hard drive, connect via USB to your PC/Laptop and power on in order to see it as an external drive. You have them in all types and flavours - support for 2,5" drives AND/OR 3,5" drives, SSD, dual docking SATA station (for quick/easy cloning)... Ofcourse, I also recommend to get one with USB3 ports/support. If you have any other MUST-HAVE! for Xmas, please let me know - I still haven't decided yet what to get (I have above already) :) images courtesy of http://blog.laptopmag.com, http://www.sharkoon.com, http://www.datapro.netThursday, January 5, 2012
Unwanted Toolbars
While I know this is old news and has been blogged/posted about a thousand times already - I still notice a lot of users having problems with an overload of toolbars they don't want/need.
More and more software (mainly free software) bundle their software package with a toolbar since it's an extra source of income.
While in some cases, a toolbar *can* be necessary or useful, always ask yourself if you really need/want this toolbar.
Additional Toolbars can slow down your browser since it takes longer to start them up, can interfere with certain webpages you want to view, can have compatibility issues with other toolbars/add-ons already installed or can even crash your entire browser.
Apart from a toolbar/BHO, some toolbars also add additional loading points (run key, service, appinit_dlls..) which may cause an extra slowdown of your computer in general.
Toolbars also take up extra space in your browser, leaving you with less content of the webpage you want to view.
Do you really want your browser to look like this?
If the answer is Yes, then I suggest you check with your eye specialist or stay away from computers and find another hobby.
Also, not all toolbars are as harmless as they look. Do you want them to monitor your browser activities? What sites you visit? Collect other info from your computer?
Do you want them to redirect searches? Change your startpage? Display Advertisements (targetted Ads)? If the answer is No, then uninstall them or don't install them in the first place.
In most cases, legit software with a toolbar bundled, offers the user the option to uncheck the toolbar during install. Too bad most have these toolbars pre-checked already, so many users who install the software just click through the installation screens (next) in a hurry and end up with toolbars they don't want or need.
And that's still the biggest mistake users make.
That's why it is always a good practice to read every part of the installation screens the software displays, so you don't miss the option where you can uncheck the toolbar or other junk during install.
Also, it's a good practice to always read the EULA/Privacy Policy when you want to install certain software.
Example:
Unfortunately, not every software bundled with a toolbar/other junk offers this option to uncheck during install. This is bad practice and such software should be avoided in the first place.
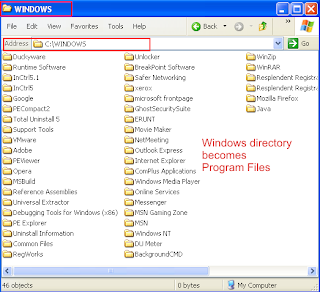
In case you have (accidentally) installed a toolbar you didn't want/need in the first place, use the Windows’ built-in "Add/Remove Programs" in the Control Panel ("Programs and Features" in Vista/Win7) and look if it's listed there so you can uninstall it.
Or, in case it's not listed there, you can disable or remove them them via your browser:
For Internet Explorer: http://technet.microsoft.com/en-us/magazine/dd364987.aspx or http://mintywhite.com/windows-7/7security/5-easy-ways-uninstall-toolbars-internet-explorer-8/
For Firefox: http://kb.mozillazine.org/Uninstalling_toolbars
For Google Chrome: http://support.google.com/chrome/bin/answer.py?hl=en&answer=113907
For Opera: Click Tools > Preferences > Advanced Tab > Toolbars (listed on the left). There you can select and delete the toolbar.
In general, if you don't use/need toolbars, uninstall them or don't install them in the first place.
Wednesday, November 30, 2011
ABN AMRO Phishing mail
Another phishing mail I received today. Looks like my mailbox attracks phishing mails this week...
This certainly gives me a reason to blog more often again ;-)
This one is targeting Dutch ABN AMRO bank account users.
------
Geachte ABN-Amro klant,
® Op dit moment is ABN-Amro bezig met het vernieuwen van de systeembeveiligingen. Hierbij vragen wij u om uw persoonsgegevens opnieuw in te vullen door op de onderstaande link te klikken
Wij zullen de gegevens verifieren en als het nodig is de aanpassingen opnieuw in het systeem opnemen. Hierna wordt telefonisch contact met u opgenomen om de gegevens te beveiigen.
------
This one is sent from the spoofed mailaddress ABN AMRO NV customercare @ abnamro.nl
When you click the Log in button, it redirects you to a phishing page where it asks you to fill in your bank account and passnumber.
It looks like there are a lot of similar phishing mails going around lately to target ABN AMRO bank account users and I fear a lot of new ones will follow.
In case you have received a similar mail from ABN AMRO, please report it via their website:
https://www.abnamro.nl/nl/overabnamro/f_aanvragen.html
Saturday, November 26, 2011
Beware Telenet.be users - Telenet.be phishing scam going around
First of all - WOW! It has been ages I have blogged here ! I really should start to blog more often again. Work & life has kept me real busy lately, so unfortunately there's not much extra free time left over anymore.
If only there were 36 hours in a day, so much I still want to do and learn...
Anyway, Just received the following in my mailbox today:
Dear 'pandora.be' E-mail User,
We are currrently upgrading our database and all account need to be verified.To complete your account activation with us, you are required to reply
to this message and enter your password in the space provided (********) you are required to do this before the next 48 hours of the receipt of this email or your database will be de-activated from our database.You are required to reply this message to telenet.be helpdesk database office on their email address: help-desk@email.com
Full Name:
username:
Password:
Thank you for using pandora.be.
Copyright 2011 © pandora.be web Team.
Stacy Williams
PANDORA.BE HELP DESK OFFICE
Hosting: Telenet Operaties N.V.
IP Address: 195.130.144.20
Telenet.be (Pandora.be is controlled by telenet.be) is one of the biggest ISPs here in Belgium
Above is a fake email and in no way associated with Telenet.be.
This mail is designed to steal your telenet.be credentials.
Telenet.be would never ask for your credentials via email, nor would any other company.
As a matter of fact, never ever give your passwords/credentials via mail, no matter who the company claims to be.
If you received this mail, delete it - certainly do not respond to it.
In case you have become a victim of this mail already and responded to it, change your password asap.
For telenet.be users, see here.
Monday, November 1, 2010
Rogue HDDDefragmenter
HDD Defragmenter is a rogue which appears quite easy to get rid of. That's not what I wanted to talk about. It's about how much Rogues have improved.
Once installed, you get the following message:
Your executables cannot launch. Clicking the 'Scan Hard Drives' button brings up the next image:
When scanning, it even has a FAKE safe mode. Desktop just goes black with the corners showing 'Safe Mode':
Next images show how convincing these rogues can be:

To get rid of it, scan with Malwarebytes or another Antivirus/Antispyware application.
Credits go to sUBs for screenshots and analysis
Saturday, October 30, 2010
Fighting Trojan Horses is a Family thing
My cousin Jimmy also fights Trojan Horses, but in a slightly different way...
More info and Biography of Jimmy here:
http://www.fmx4ever.com/clanky/team/jimmy-verburgh/
https://www.facebook.com/jimbo199/
Monday, November 2, 2009
IOBit Steals Malwarebytes’ Intellectual Property
Malwarebytes has recently uncovered evidence that a company called IOBit based in China is stealing and incorporating our proprietary database and intellectual property into their software. We know this will sound hard to believe, because it was hard for us to believe at first too. But after an indepth investigation, we became convinced it was true. Here is how we know.
We came across a post on the IOBit forums (cached version since they deleted the thread - well, now the cached version got deleted as well. Glad I still have a screenshot, see below) that showed IOBit Security 360 flagging a specific key generator for our Malwarebytes’ Anti-Malware software using the exact naming scheme we use to flag such keygens: Don’t.Steal.Our.Software.A.
Dont.Steal.Our.Software.A, File, G:\Nothing Much\Anti-Spyware\Malwarebytes’ Anti-Malware v1.39\Key_Generator.exe, 9-30501
Why would IOBit detect a keygen for our software and refer to it using our database name? We quickly became suspicious. Either the forum post was fraudulent or IOBit was stealing our database.
So we dug further. We accumulated more similar evidence for other detections, and we soon became convinced that this was not a mistake, it was not a coincidence, it was not an isolated event, and it persisted presently in their current database. They are using both our database and our database format exactly.
The final confirmation of IOBit’s theft occurred when we added fake definitions to our database for a fake rogue application we called Rogue.AVCleanSweepPro. This “malware” does not actually exist: we made it up. We even manufactured fake files to match the fake definitions. Within two weeks IOBit was detecting these fake files under almost exactly these fake names.
We can’t publicly show all the evidence we found, because it is still our intellectual property: proprietary information about our database internals. But we don’t want you to have to take our word for it either, so we found a way to show you an example illustrating an indisputable pattern of theft.
Consider the file, dummy.exe. It is a harmless dummy executable that runs, displays a “Hello World” message box, and exits. You can see from third-party scans on VirusTotal, that no other security vendor flags this executable as malicious or even suspicious.
We created this dummy executable, then manipulated it slightly so that it matches one of the signatures in our database. We emphasize that it is still not malicious! — the signature is perfectly benign, when not in the context of actual malware, as you can see from the VirusTotal results.
We scanned the file with our own Malwarebytes’ Anti-Malware software and indeed it was flagged as “Don’t.Steal.Our.Software.A”. We scanned it with IOBit using their current build and database version and it was flagged as the same “Don’t.Steal.Our.Software.A”. We have included log file file and a screenshot of the detection. You can verify by yourself using the dummy executable and their most recent database.
We have attached two other such dummy executables to this post, so you can see for yourself. One of them, “rogue.exe”, matches our fake Rogue.AVCleanSweepPro (screenshot) definition, the other “fake.exe”, matches our Adware.NaviPromo definition (screenshot). VirusTotal results for “fake.exe” and “rogue.exe” so you can see they are benign. You can see a screenshot of our detections here.
During the course of our investigation, we uncovered additional evidence that IOBit may have stolen the proprietary databases of other security vendors as well. We are in the process of contacting these vendors.
Malwarebytes intends to pursue legal action against IOBit. We demand IOBit immediately remove all traces of Malwarebytes’ proprietary research and database from their software. We also demand IOBit be delisted from Download.com due to Terms of Service violations. This is criminal: it is theft, it is fraud, and we will not stand for it.
What can you do to help? If you feel the same way we do about this theft, we encourage you to send an email to hosting services such as Download.com and Majorgeeks.com requesting that all IOBit software be removed.
Copy/paste of the original Article here
Update to this post: IOBit’s Denial of Theft Unconvincing










